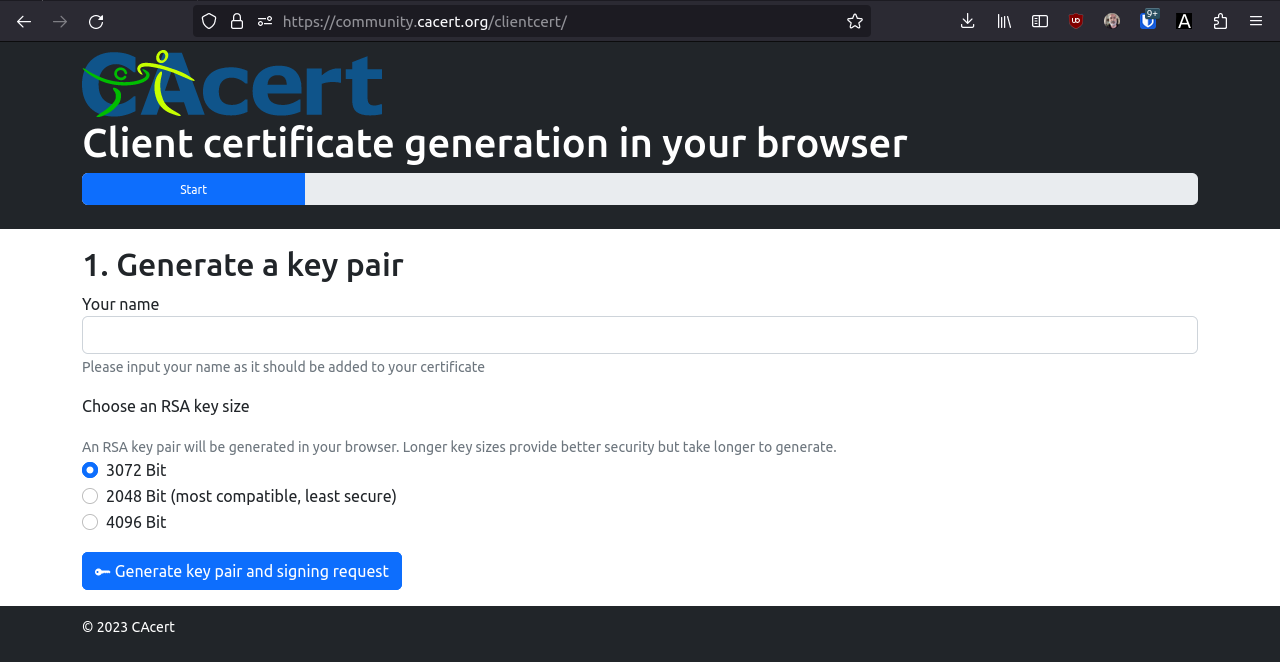
Since Google and Mozilla have removed the <keygen> element we use from the HTML standard and from their browsers, we have endeavoured to provide a valid replacement so that client certificates can once again be created so easily that even my grandmother could do it.

Finding a solution was not easy; other CAs were also sweating bullets here. The solution that we have been offering for some time now was initially somewhat hidden, but has since been prominently linked as the seventh service on our community portal community.cacert.org.
Both the new solution and the community portal are the result of the tireless work of a small group of volunteers. As a small thank you, you can make their work easier by not having to worry about CAcert’s operating costs. Donation account CAcert: IBAN CH02 0077 4010 3947 4420 0 or with bank or credit card.